What is the line of death and why should you care about it?
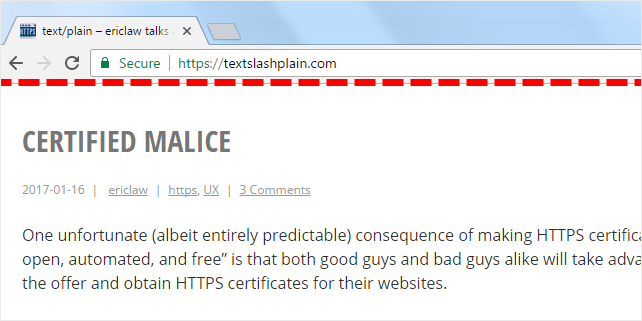
Security UI is hard. That’s why, security designers have a real challenge when creating applications that display untrusted content. Their goal is to prevent potential attackers to take full control of a block of pixels (and turn the UI into anything they want and expose users to unsafe actions).
In web browsers, usually it works this way: the browser controls the top area and the pixels located under the top area are controlled by the site itself. This is what we call the line of death.

If users trust pixels above the line of death, they will probably think that they are in a safe area. If they are somehow convinced to trust the UI below the line of death, they’ll probably be in trouble.
Trusting the content below the line of death might kill your security. Moreover, there could also be unsafe areas above the line. These are so-called zones of death. Let’s identify them:
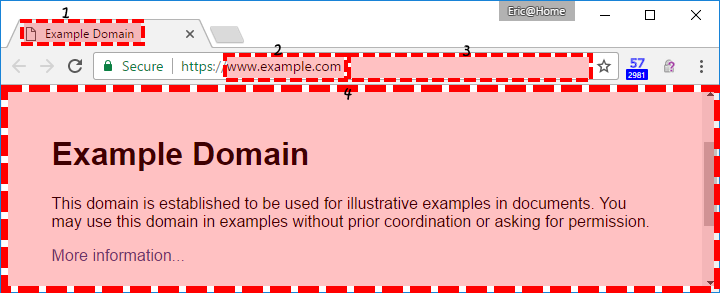
Zone 1
Web page title and icon. This info is fully controlled by the attacker and may include deceptive content.
Zone 2
The domain name. Apparently, this seems like a trustworthy component of the URL. However, if you access this domain: https://paypal-account.com/ you really get it loaded, but it has no relationship with the legitimate service that can be accessed at https://paypal.com/.
Zone 3
The path component of the URL. This is fully untrustworthy area. Example: http://account-update.com/paypal.com/ has nothing to do with the the legitimate service Paypal.
Zone 4
Nothing in this area is safe and to be believed. In windowed OSs, it creates the possibility of picture-in-picture attacks, where the whole browser window can be faked.

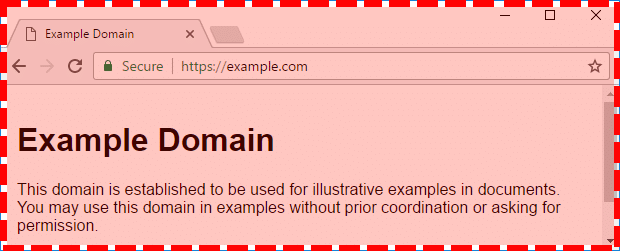
It gets even more unsafe because of Fullscreen API introduced in HTML5. This means that the zone of death looks like this:
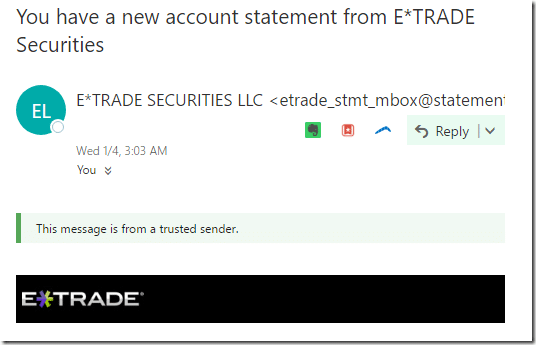
The concept of the line of death is related to other web applications as well. This is how Outlook.com renders an email:

The user gets a “This message is from a trusted sender.” notice, which is located inside the zone of death.
Read more about the line of death, explore examples and real stories in this article.